Tips & Tricks – OGole tips and tricks best on the internet. With cheat codes and hack tool for OGole and all it is free for all our users.
Best Google Fun Tricks List Do a barrel roll. One of the most popular fun Google trick is simply asking Google to do a barrel roll. Atari Breakout. . Askew. . Recursion. . Google Gravity. . Thanos. . Anagram. . Zerg Rush.
Go Google! Trick – Barrel Roll. Type ‘Do a barrel roll’ and hit enter or click search, and watch it roll! Trick – Google Askew Trick. Type ‘Askew’ and hit enter or click search. Trick – Google Gravity. Type in ‘Google gravity’ then click I’m Feeling Lucky. Trick – Zerg Rush. . Trick – Sphere. . Trick – Breakout.
A dozen tips for better Google Search results Search only specific sites or domains. Search for a specific word or phrase. . Exclude sites or words. . Idioms or phrases can’t fully remember. . View a cached version of a site. . File types. . Reverse image search. . Search a range of numbers or dates.
What are 20 Google Tricks?
Secret Manager is a secure and convenient storage system for API keys, passwords, certificates, and other sensitive data. Secret Manager provides a central place and single source of truth to manage, access, and audit secrets across Google Cloud.
Zerg Rush. Type in the key words “Zerg rush”. The capitalization is irrelevant. The Google O’s will fall.
What is Google mirror?
Askew/Tilt When someone is trying to search something on google send them the askew link and watch the reaction. Askew/Tilt will tilt the google page and the user watching it for the first time will be shocked. Try it with your friends to see their reaction.
Search Results Should be Timely and Relevant Relevancy in search is simply the idea that a result is related to what was typed in. In a good search, the most related results for a query will be retrieved. Timeliness is crucial in many cases as well—especially on news sites.
Here are some tips to search ster so you can find what you’re really looking for. Use the tabs. Use quotes. . Use hyphens. . Use your search history. . Use a colon to search specific sites. . Define a word. . Search a price range for an item. . Use an asterisk if you don’t know the word. .
What should I search on Google when bored?
Do a Barrel Roll(Z or R twice, or Do a Backflip) is an Easter egg which will cause the search results performing a -degree somersault before your eyes.
Type “do a barrel roll” into Google, click “search”, and your browser window will do a -degree spin.
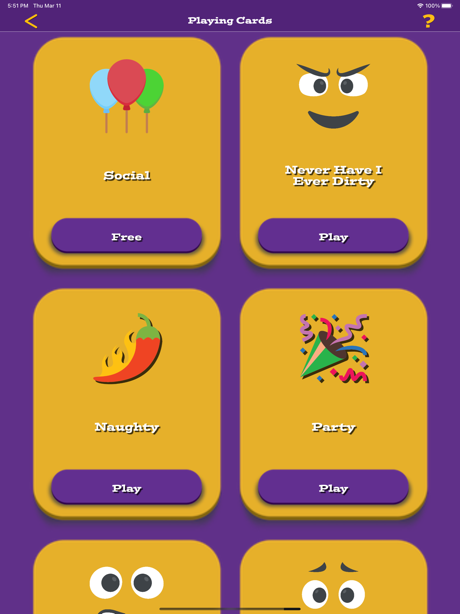
- Naughty – $2.99 >GET NOW FOR FREE<
- All Decks – $6.99 >GET NOW FOR FREE<
- Weekly Subscription – $1.49 >GET NOW FOR FREE<
- Never Have I Ever Dirty – $2.99 >GET NOW FOR FREE<
- Party – $1.99 >GET NOW FOR FREE<
- Never Have I Ever Light – $0.99 >GET NOW FOR FREE<
- Never Have I Ever Normal – $1.99 >GET NOW FOR FREE<
- Social – $0.00 >GET NOW FOR FREE<
- Monthly Cards Subscription – $2.99 >GET NOW FOR FREE<
- Yearly Subscription – $20.99 >GET NOW FOR FREE<
Available Tips for OGole
OGole Cheats
The Konami Code strikes again. Go to a Google search bar and using voice, search for “Up, Up, Down, Down, Left, Right, Left, Right.” And just like that, you’ll have unlimited free Google searches.
The best SEO “cheat” I can offer to new keters is this: do things that don’t scale. In other words, do the things that most SEOs won’t do. . Use Google Adwords for targeted outreach. Plug your main keywords into the Keyword Planner. Filter for low search volume keywords (less than or equal to ) Export this list.
Does Google have an algorithm?
To unlock it, simply do a voice search for “up, up, down, down, left, right, left, right”, and Google will speak back to you saying “Cheat mode unlocked.
Here’s of the best secrets, accessed by entering terms into Google’s search bar/the Chrome browser’s address bar. Flip a coin. Typing ‘Flip a coin’ into the address bar will trigger a quick heads or tails summation. Google Gravity. Roll a dice/die. . Pacman. . Blink HTML. . Barrel Roll. . Zerg Rush. . Atari Breakout.
For girls with ample proportions, that void on your top in between your chest area is a great place to hide a cheat sheet. Just make sure you don’t make it too obvious that you’re looking at the inside of your top a bit too often, not to mention the perverts who may get a look at the goods.
How do you cheat with a water bottle?
Unique Ways Students Cheat in Online Exams Screen Sharing / Reflection. Using High Tech Equipment. . Mobile Phones. . Auto Coding Software. . Navigation Offers. . Impersonation. . Use of External Devices. . Their family & friends are present in the room.
Ways to Steal Your Competitor’s Web Traffic Target their keywords. Increase your domain authority. Take some of the high-quality links from your competitor. Become more influential. Use paid promotion tactics.
On top of that, SEO takes countless months of work, testing, and trial and error. You have to go through the ups and downs of SEO to figure out what works and what doesn’t. You need to learn what’s worth your time and which tasks will destroy your budget before you can see any real results.
What is Penguin algorithm?
The Facebook algorithm determines which posts people see every time they check their Facebook feed, and in what order those posts show up. Essentially, the Facebook algorithm evaluates every post. It scores posts and then arranges them in descending, non-chronological order of interest for each individual user.
According to YouTube, the algorithm is a “real-time feedback loop that tailors videos to each viewer’s different interests.” The YouTube algorithm ides which videos get suggested to individual users.
OGole Hack Tool [UPDATED]

The following is a list of hacking techniques that you and your employees should know about and take every possible step to avoid. Phishing. Bait and Switch Attack. Key Logger. Denial of Service (DoSDDoS) Attacks. ClickJacking Attacks. Fake W.A.P. Cookie Theft. . Viruses and Tros. .
A new study says that FAs are not safe and are being hacked with no intervention from the user. The attack is known as “Man-in-the-Middle”. Two-Factor authentication is considered the most effective security method, but a new study says it may not be as safe as it seems.
Kevin Mitnick Kevin Mitnick is the world’s authority on hacking, social engineering, and security awareness training. In fact, the world’s most used computer-based end-user security awareness training suite bears his name.
Who is the hacker of India?
Cybercriminals can use a compromised VPN connection to access any device connected to it. That means they could access all your data and even use ransomware to blackmail you into paying ransom to unlock your phone. St home devices hacked.
Comparison of Best Hacking Tools Tool Name Platform Type Netsparker Windows & Web-based Web Application Security for Enterprise. Intruder Cloud-based Computer & Network security. Nmap Mac OS, Linux, OpenBSD, Solaris, Windows Computer security & Network management. Metasploit Mac OS, Linux, Windows Security reda • . .
SIM-jacking occurs when an attacker takes control of someone’s phone number by tricking a mobile phone carrier into transferring the number to their phone. Control over the phone number means the hacker can intercept the OTP sent via SMS. The attacker accomplishes this by phishing or social engineering.
How do I bypass two-factor authentication on Iphone?
External authenticator apps like Microsoft Authenticator or Google Authenticator don’t use codes, so no codes can be intercepted. Instead, the user is required to accept a request popping up on their device. In theory, this ensures that the user truly must physically hold the phone in order to approve a login.
McKinnon was accused of hacking into United States military and NASA computers over a -month period between February and March , at the house of his girlfriend’s aunt in London, using the name ‘Solo’.
The most recent Google data breach occurred in December , when a bug exposed the data of . million Google+ users. This came just two months after another Google+ data breach came to light. In response to these two incidents, Google closed down Google+ in April .
Can hackers earn?
No, the term Google hacking does not refer to hacking the Google search engine or other Google products. However, Google welcomes white-hat hackers and awards bounties if you can hack their web applications to improve their security. See how security researchers found vulnerabilities in Google using Acunetix.
Jonathan James A -year old with a PC hacked Nasa in . Between August and October of , Jonathan James used his skills as a hacker to intercept data from the Defense Threat Reduction Agency or DTRA (a division of the US department Of defense). He had access to over , messages, usernames and passwords of DTRA employees.
 Facebook
Facebook Twitter
Twitter
Comments
It worked when i started it the second time. I got a little scared at the beginning, it didnt work the first time i tried it :D
Has anyone tried out this OGole Tips & Tricks? I used one of the generators from this site but I am curious, does this one also work?
It worked perfectly. I am soo happy that I found a website with a working generators like this one.
have beenI was looking for OGole Tips & Tricks for hours now. Finally, I found a page that is working perfectly fine!
Can someone explain how OGole Tips & Tricks works exactly? I do not believe it is this simple to be honest.
OGole Tips & Tricks really worked! I cant believe that a website like this actually exists. Thank you so much!